Detecting IP-tracking proof interfaces by looking for NATs
Aurélien Buchet , Peter Snyder , Hamed Haddadi and Cristel Pelsser
This 2023 conference poster, by Aurélien Buchet and 3 coauthors, was presented at 2023 7th Network Traffic Measurement and Analysis Conference (TMA). Topics covered include performance evaluation, privacy, costs, telecommunication traffic, virtual private networks, browsers, and ip networks.
Full author list: Aurélien Buchet, Peter Snyder, Hamed Haddadi, and Cristel Pelsser.
Abstract
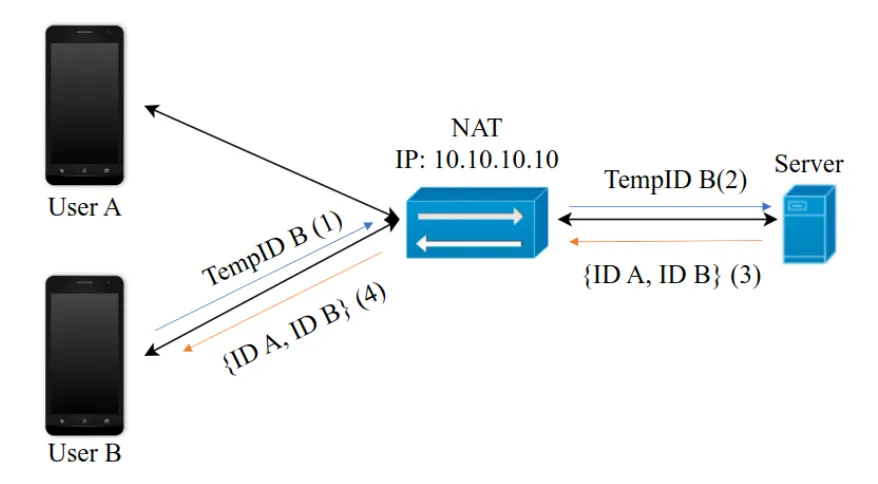
In this poster, we propose an approach based on short-lived random identifiers to allow applications to detect when multiple users share the same IP address such as when they are behind NATs. Using NATed interfaces could provide a cheap way to evade IP-based tracking as the traffic of all users is merged into a single IP flow. As a result, it is harder for trackers to single out (and so re-identify by IP address) users behind a NAT. For many years, there has been a race between web trackers trying to find techniques to monitor user behaviour online, and privacy researchers looking for solutions to avoid such tracking. Despite progresses in browser privacy-preserving techniques, IP tracking is still highly effective because current solutions to hide an IP address such as VPNs, or the Tor network, rely on external services and often induce a high cost in terms of performance. Our proposal could lead to solutions that are cheaper to deploy and don't affect the performance as much. We developed an Android application detecting when an IP address was shared by multiple devices and reported the availability of such interfaces. We show that it is possible to identify networks where multiple users share the same IP address. We also discuss how our system can be protected from potential attackers.
Publication Details
- Publication Type
- poster
- Publication Date
- June 2023
- Published In
- 2023 7th Network Traffic Measurement and Analysis Conference (TMA)
- Pages
- 1–4
- Digital Object Identifier (DOI)
- 10.23919/TMA58422.2023.10198950
Suggested citation
Aurélien Buchet, Peter Snyder, Hamed Haddadi, and Cristel Pelsser. 2023. Detecting IP-tracking proof interfaces by looking for NATs. In 2023 7th Network Traffic Measurement and Analysis Conference (TMA). 1–4. https://doi.org/10.23919/TMA58422.2023.10198950
BibTeX Citation
BibTeX Citation
@poster{Buchet2023,
title = {Detecting IP-tracking proof interfaces by looking for NATs},
author = {Buchet, Aurélien and Snyder, Peter and Haddadi, Hamed and Pelsser, Cristel},
year = 2023,
month = jun,
booktitle = {2023 7th Network Traffic Measurement and Analysis Conference ({TMA})},
pages = {1--4},
doi = {10.23919/TMA58422.2023.10198950},
abstract = {In this poster, we propose an approach based on short-lived random identifiers to allow applications to detect when multiple users share the same IP address such as when they are behind NATs. Using NATed interfaces could provide a cheap way to evade IP-based tracking as the traffic of all users is merged into a single IP flow. As a result, it is harder for trackers to single out (and so re-identify by IP address) users behind a NAT. For many years, there has been a race between web trackers trying to find techniques to monitor user behaviour online, and privacy researchers looking for solutions to avoid such tracking. Despite progresses in browser privacy-preserving techniques, IP tracking is still highly effective because current solutions to hide an IP address such as VPNs, or the Tor network, rely on external services and often induce a high cost in terms of performance. Our proposal could lead to solutions that are cheaper to deploy and don't affect the performance as much. We developed an Android application detecting when an IP address was shared by multiple devices and reported the availability of such interfaces. We show that it is possible to identify networks where multiple users share the same IP address. We also discuss how our system can be protected from potential attackers.},
groups = {Posters},
keywords = {Performance evaluation,Privacy,Costs,Telecommunication traffic,Virtual private networks,Browsers,IP networks}
}
Related publications
Minimum Backup Configuration-Creation Method for IP Fast Reroute
Shohei Kamamura, Takashi Miyamura, and Cristel Pelsser, et al.
GLOBECOM 2009 - 2009 IEEE Global Telecommunications Conference, 2009
The Art of Detecting Forwarding Detours
Julián Martín Del Fiore, Valerio Persico, and Pascal Mérindol, et al.
IEEE Transactions on Network and Service Management TNSM, 2021
Filtering the Noise to Reveal Inter-Domain Lies
Julián Martín Del Fiore, Pascal Mérindol, and Valerio Persico, et al.
2019 Network Traffic Measurement and Analysis Conference (TMA), 2019
Chocolatine: Outage Detection for Internet Background Radiation
Andreas Guillot, Romain Fontugne, and Philipp Winter, et al.
2019 Network Traffic Measurement and Analysis Conference (TMA), 2019