A System to Detect Forged-Origin Hijacks
Thomas Holterbach , Thomas Alfroy , Amreesh Phokeer , Alberto Dainotti and Cristel Pelsser
This 2024 international conference paper, by Thomas Holterbach and 4 coauthors, was presented at 21th USENIX Symposium on Networked Systems Design and Implementation (NSDI 24).
Full author list: Thomas Holterbach, Thomas Alfroy, Amreesh Phokeer, Alberto Dainotti, and Cristel Pelsser.
Abstract
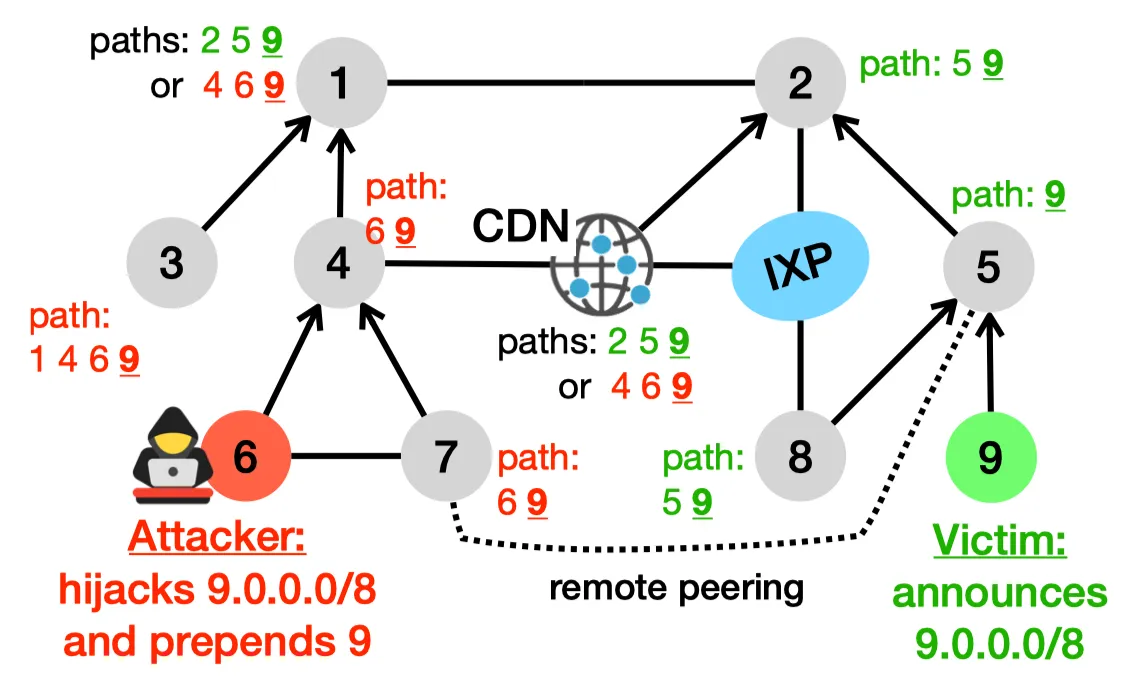
Despite global efforts to secure Internet routing, attackers still successfully exploit the lack of strong BGP security mechanisms. This paper focuses on an attack vector that is frequently used: Forged-origin hijacks, a type of BGP hijack where the attacker manipulates the AS path to make it immune to RPKI-ROV filters and appear as legitimate routing updates from a BGP monitoring standpoint. Our contribution is DFOH, a system that quickly and consistently detects forgedorigin hijacks in the whole Internet. Detecting forged-origin hijacks boils down to inferring whether the AS path in a BGP route is legitimate or has been manipulated. We demonstrate that current state-of-art approaches to detect BGP anomalies are insufficient to deal with forged-origin hijacks. We identify the key properties that make the inference of forged AS paths challenging, and design DFOH to be robust against real-world factors (e.g., data biases). Our inference pipeline includes two key ingredients: (i) a set of strategically selected features, and (ii) a training scheme adapted to topological biases. DFOH detects 90.9% of the forged-origin hijacks within only ≈5min. In addition, it only reports ≈17.5 suspicious cases every day for the whole Internet, a small number that allows operators to investigate the reported cases and take countermeasures.
Publication Details
- Publication Type
- Conference Paper
- Publication Date
- 2024
- Published In
- 21th USENIX Symposium on Networked Systems Design and Implementation (NSDI 24)
- Publisher
- USENIX Association
Suggested citation
Thomas Holterbach, Thomas Alfroy, Amreesh Phokeer, Alberto Dainotti, and Cristel Pelsser. 2024. A System to Detect Forged-Origin Hijacks. In 21th USENIX Symposium on Networked Systems Design and Implementation (NSDI 24). USENIX Association.
BibTeX Citation
BibTeX Citation
@inproceedings{Holterbach2024,
title = {A System to Detect Forged-Origin Hijacks},
author = {Thomas Holterbach and Thomas Alfroy and Amreesh Phokeer and Alberto Dainotti and Cristel Pelsser},
year = 2024,
booktitle = {21th USENIX Symposium on Networked Systems Design and Implementation ({NSDI} 24)},
publisher = {USENIX Association},
abstract = {Despite global efforts to secure Internet routing, attackers still successfully exploit the lack of strong BGP security mechanisms. This paper focuses on an attack vector that is frequently used: Forged-origin hijacks, a type of BGP hijack where the attacker manipulates the AS path to make it immune to RPKI-ROV filters and appear as legitimate routing updates from a BGP monitoring standpoint. Our contribution is DFOH, a system that quickly and consistently detects forgedorigin hijacks in the whole Internet. Detecting forged-origin hijacks boils down to inferring whether the AS path in a BGP route is legitimate or has been manipulated. We demonstrate that current state-of-art approaches to detect BGP anomalies are insufficient to deal with forged-origin hijacks. We identify the key properties that make the inference of forged AS paths challenging, and design DFOH to be robust against real-world factors (e.g., data biases). Our inference pipeline includes two key ingredients: (i) a set of strategically selected features, and (ii) a training scheme adapted to topological biases. DFOH detects 90.9% of the forged-origin hijacks within only ≈5min. In addition, it only reports ≈17.5 suspicious cases every day for the whole Internet, a small number that allows operators to investigate the reported cases and take countermeasures.},
groups = {International Conferences}
}
Related publications
The Next Generation of BGP Data Collection Platforms
Thomas Alfroy, Thomas Holterbach, and Thomas Krenc, et al.
Proceedings of the ACM SIGCOMM 2024 Conference, 2024
Measuring Internet Routing from the Most Valuable Points
Thomas Alfroy, Thomas Holterbach, and Thomas Krenc, et al.
2024
Internet Science Moonshot: Expanding BGP Data Horizons
Thomas Alfroy, Thomas Holterbach, and Thomas Krenc, et al.
Proceedings of the 22nd ACM Workshop on Hot Topics in Networks HotNets, 2023
MVP: Measuring Internet Routing from the Most Valuable Points
Thomas Alfroy, Thomas Holterbach, and Cristel Pelsser
Poster in the Proceedings of the Internet Measurement Conference (IMC), 2022