BGP Communities: Even more Worms in the Routing Can
Florian Streibelt , Franziska Lichtblau , Robert Beverly , Anja Feldmann , Cristel Pelsser , Georgios Smaragdakis and Randy Bush
This 2018 international conference paper, by Florian Streibelt and 6 coauthors, was presented at Proceedings of the Internet Measurement Conference 2018, IMC 2018. Topics covered include bgp, routing security, internet routing, blackholing, hijacking, and security.
Full author list: Florian Streibelt, Franziska Lichtblau, Robert Beverly, Anja Feldmann, Cristel Pelsser, Georgios Smaragdakis, and Randy Bush.
Abstract
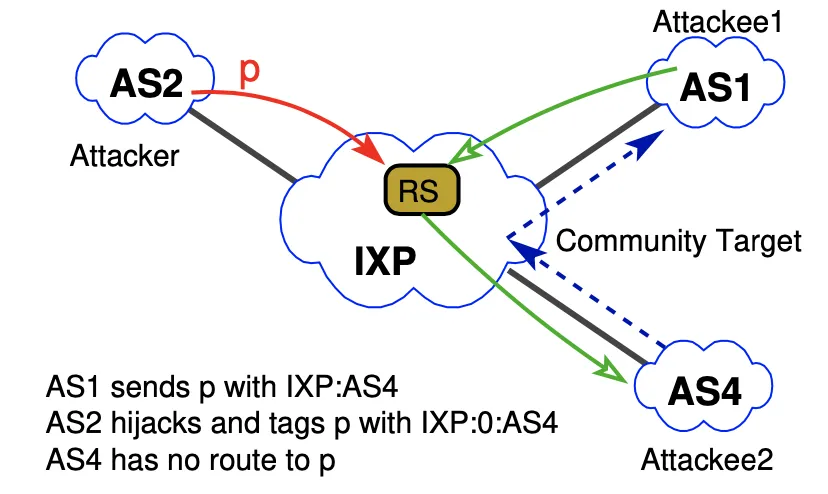
BGP communities are a mechanism widely used by operators to manage policy, mitigate attacks, and engineer traffic; e.g., to drop unwanted traffic, filter announcements, adjust local preference, and prepend paths to influence peer selection. Unfortunately, we show that BGP communities can be exploited by remote parties to influence routing in unintended ways. The BGP community-based vulnerabilities we expose are enabled by a combination of complex policies, error-prone configurations, a lack of cryptographic integrity and authenticity over communities, and the wide extent of community propagation. Due in part to their ill-defined semantics, BGP communities are often propagated far further than a single routing hop, even though their intended scope is typically limited to nearby ASes. Indeed, we find 14% of transit ASes forward received BGP communities onward. Given the rich inter-connectivity of transit ASes, this means that communities effectively propagate globally. As a consequence, remote adversaries can use BGP communities to trigger remote blackholing, steer traffic, and manipulate routes even without prefix hijacking. We highlight examples of these attacks via scenarios that we tested and measured both in the lab as well as in the wild. While we suggest what can be done to mitigate such ill effects, it is up to the Internet operations community whether to take up the suggestions.
Publication Details
- Publication Type
- Conference Paper
- Publication Date
- October 2018
- Published In
- Proceedings of the Internet Measurement Conference 2018, IMC 2018
- Pages
- 279–292
- Publisher
- ACM
- Location
- Boston, MA, USA
- Digital Object Identifier (DOI)
- 10.1145/3278532.3278557
- External Link
- https://dl.acm.org/citation.cfm?id=3278557
Suggested citation
Florian Streibelt, Franziska Lichtblau, Robert Beverly, Anja Feldmann, Cristel Pelsser, Georgios Smaragdakis, and Randy Bush. 2018. BGP Communities: Even more Worms in the Routing Can. In Proceedings of the Internet Measurement Conference 2018, IMC 2018. ACM, Boston, MA, USA, 279–292. https://doi.org/10.1145/3278532.3278557
BibTeX Citation
BibTeX Citation
@inproceedings{Streibelt2018,
title = {BGP Communities: Even more Worms in the Routing Can},
author = {Florian Streibelt and Franziska Lichtblau and Robert Beverly and Anja Feldmann and Cristel Pelsser and Georgios Smaragdakis and Randy Bush},
year = 2018,
month = oct,
booktitle = {Proceedings of the Internet Measurement Conference 2018, {IMC} 2018},
publisher = {ACM},
address = {Boston, MA, USA},
pages = {279--292},
doi = {10.1145/3278532.3278557},
url = {https://dl.acm.org/citation.cfm?id=3278557},
abstract = {
BGP communities are a mechanism widely used by operators to manage policy, mitigate attacks, and engineer traffic; e.g., to drop unwanted traffic, filter announcements, adjust local preference, and prepend paths to influence peer selection.
Unfortunately, we show that BGP communities can be exploited by remote parties to influence routing in unintended ways. The BGP community-based vulnerabilities we expose are enabled by a combination of complex policies, error-prone configurations, a lack of cryptographic integrity and authenticity over communities, and the wide extent of community propagation. Due in part to their ill-defined semantics, BGP communities are often propagated far further than a single routing hop, even though their intended scope is typically limited to nearby ASes. Indeed, we find 14% of transit ASes forward received BGP communities onward. Given the rich inter-connectivity of transit ASes, this means that communities effectively propagate globally. As a consequence, remote adversaries can use BGP communities to trigger remote blackholing, steer traffic, and manipulate routes even without prefix hijacking. We highlight examples of these attacks via scenarios that we tested and measured both in the lab as well as in the wild. While we suggest what can be done to mitigate such ill effects, it is up to the Internet operations community whether to take up the suggestions.
},
bibsource = {dblp computer science bibliography, https://dblp.org},
biburl = {https://dblp.org/rec/conf/imc/StreibeltLBFPSB18.bib},
groups = {International Conferences},
keywords = {BGP, routing security, Internet routing, blackholing, hijacking, security},
type = {Selective conference},
x-international-audience = {Yes},
x-language = {EN},
award = {Applied Networking Research Prize (ANRP)}
}
Related publications
The Origin of BGP Duplicates
D. Hauweele, B. Quoitin, and Cristel Pelsser, et al.
CoRes, 2016
Enforcing RPKI-based routing policy on the data plane at an internet exchange
Josh Bailey, Dean Pemberton, and Andy Linton, et al.
Proceedings of the third workshop on Hot topics in software defined networking, HotSDN '14, 2014
Enforcing RPKI-Based Routing Policy on the Data Plane at an Internet Exchange
Josh Bailey, Dean Pemberton, and Andy Linton, et al.
HotSDN 2014 (Poster session), 2014
The Next Generation of BGP Data Collection Platforms
Thomas Alfroy, Thomas Holterbach, and Thomas Krenc, et al.
Proceedings of the ACM SIGCOMM 2024 Conference, 2024