Verification of Cloud Security Policies
Loïc Miller , Pascal Mérindol , Antoine Gallais and Cristel Pelsser
This 2021 international conference paper, by Loïc Miller and 3 coauthors, was presented at IEEE International Conference on High Performance Switching and Routing Conference (HPSR). Topics covered include policy verification, metagraphs, policymodeling, rego, access control, and authorization.
Full author list: Loïc Miller, Pascal Mérindol, Antoine Gallais, and Cristel Pelsser.
Abstract
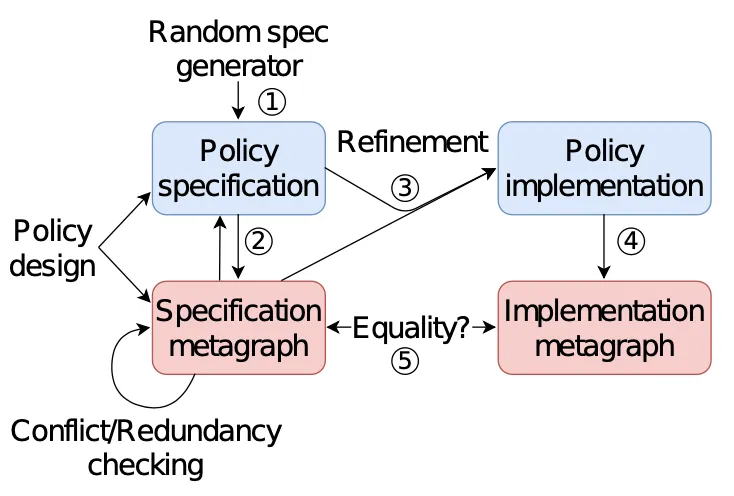
Companies like Netflix increasingly use the cloud to deploy their business processes. Those processes often involve partnerships with other companies, and can be modeled as workflows where the owner of the data at risk interacts with contractors to realize a sequence of tasks on the data to be secured. In practice, access control is an essential building block to deploy these secured workflows. This component is generally managed by administrators using high-level policies meant to represent the requirements and restrictions put on the workflow. Handling access control with a high-level scheme comes with the benefit of separating the problem of specification, i.e. defining the desired behavior of the system, from the problem of implementation, i.e. enforcing this desired behavior. However, translating such high-level policies into a deployed implementation can be error-prone. Even though semi-automatic and automatic tools have been proposed to assist this translation, policy verification remains highly challenging in practice. In this paper, our aim is to define and propose structures assisting the checking and correction of potential errors introduced on the ground due to a faulty translation or corrupted deployments. In particular, we investigate structures with formal foundations able to naturally model policies. Metagraphs, a generalized graph theoretic structure, fulfill those requirements: their usage enables to compare high-level policies to their implementation. In practice, we consider Rego, a language used by companies like Netflix and Plex for their release process, as a valuable representative of most common policy languages. We propose a suite of tools transforming and checking policies as metagraphs, and use them in a global framework to show how policy verification can be achieved with such structures. Finally, we evaluate the performance of our verification method.
Publication Details
- Publication Type
- Conference Paper
- Publication Date
- January 2021
- Published In
- IEEE International Conference on High Performance Switching and Routing Conference (HPSR)
- Digital Object Identifier (DOI)
- 10.1109/hpsr52026.2021.9481870
- External Link
- http://icube-publis.unistra.fr/4-MMGP21a
Suggested citation
Loïc Miller, Pascal Mérindol, Antoine Gallais, and Cristel Pelsser. 2021. Verification of Cloud Security Policies. In IEEE International Conference on High Performance Switching and Routing Conference (HPSR). https://doi.org/10.1109/hpsr52026.2021.9481870
BibTeX Citation
BibTeX Citation
@inproceedings{Miller2021a,
title = {Verification of Cloud Security Policies},
author = {Miller, Loïc and Mérindol, Pascal and Gallais, Antoine and Pelsser, Cristel},
year = 2021,
month = jan,
booktitle = {IEEE International Conference on High Performance Switching and Routing Conference (HPSR)},
doi = {10.1109/hpsr52026.2021.9481870},
url = {http://icube-publis.unistra.fr/4-MMGP21a},
abstract = {Companies like Netflix increasingly use the cloud to deploy their business processes. Those processes often involve partnerships with other companies, and can be modeled as workflows where the owner of the data at risk interacts with contractors to realize a sequence of tasks on the data to be secured. In practice, access control is an essential building block to deploy these secured workflows. This component is generally managed by administrators using high-level policies meant to represent the requirements and restrictions put on the workflow. Handling access control with a high-level scheme comes with the benefit of separating the problem of specification, i.e. defining the desired behavior of the system, from the problem of implementation, i.e. enforcing this desired behavior. However, translating such high-level policies into a deployed implementation can be error-prone. Even though semi-automatic and automatic tools have been proposed to assist this translation, policy verification remains highly challenging in practice. In this paper, our aim is to define and propose structures assisting the checking and correction of potential errors introduced on the ground due to a faulty translation or corrupted deployments. In particular, we investigate structures with formal foundations able to naturally model policies. Metagraphs, a generalized graph theoretic structure, fulfill those requirements: their usage enables to compare high-level policies to their implementation. In practice, we consider Rego, a language used by companies like Netflix and Plex for their release process, as a valuable representative of most common policy languages. We propose a suite of tools transforming and checking policies as metagraphs, and use them in a global framework to show how policy verification can be achieved with such structures. Finally, we evaluate the performance of our verification method.},
groups = {International Conferences},
keywords = {policy verification, metagraphs, policymodeling, rego, access control, authorization},
x-international-audience = {Yes},
x-language = {EN}
}
Related publications
De l’Utilisation des Métagraphes pour la Vérification de Politiques de Sécurité
Loïc Miller, Pascal Mérindol, and Antoine Gallais, et al.
AlgoTel, 2021
Towards Secure and Leak-Free Workflows Using Microservice Isolation
Loïc Miller, Pascal Mérindol, and Antoine Gallais, et al.
IEEE International Conference on High Perfor- mance Switching and Routing Conference (HPSR), 2021
Protection contre les fuites de données : un environnement micro-services sécurisé
Loïc Miller, Pascal Mérindol, and Antoine Gallais, et al.
CoRes, 2021
Deploying Near-Optimal Delay-Constrained Paths with Segment Routing in Massive-Scale Networks
Jean-Romain Luttringer, Thomas Alfroy, and Pascal Mérindol, et al.
Computer Networks, 2022