A Taxonomy of Attacks Using BGP Blackholing
This 2019 international conference paper, by Loïc Miller and Cristel Pelsser, was presented at European Symposium on Research in Computer Security. Topics covered include bgp, security, blackholing, ddos, communities, hijacks, and leaks.
Abstract
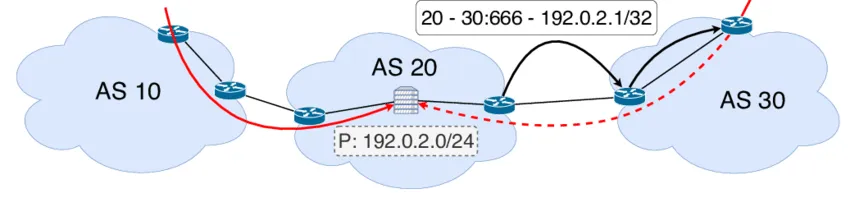
BGP blackholing is a common technique used to mitigate DDoS attacks. Generally, the victim sends in a request for traffic to the attacked IP(s) to be dropped. Unfortunately, remote parties may misuse blackholing [29, 57] and send requests for IPs they do not own, turning a defense technique into a new attack vector. As DDoS attacks grow in number, blackholing will only become more popular, creating a greater risk this service will be exploited. In this work, we develop a taxonomy of attacks combining hijacks with blackholing: BGP blackjacks (blackhole hijacks). We show that those attacks effectively grant more reach and stealth to the attacker than regular hijacks, and assess the usability of those attacks in various security deployments. We then find that routing security mechanisms for BGP [30, 31] do not provide an adequate protection against some of those attacks, and propose additional mechanisms to properly defend against or mitigate them.
Publication Details
- Publication Type
- Conference Paper
- Publication Date
- September 2019
- Published In
- European Symposium on Research in Computer Security
- Volume & Issue
- Vol. 11735
- Pages
- 107–127
- Publisher
- Springer
- Location
- Luxembourg
- Digital Object Identifier (DOI)
- 10.1007/978-3-030-29959-0_6
Suggested citation
Loïc Miller and Cristel Pelsser. 2019. A Taxonomy of Attacks Using BGP Blackholing. In European Symposium on Research in Computer Security. Springer, Luxembourg, 107–127. https://doi.org/10.1007/978-3-030-29959-0_6
BibTeX Citation
BibTeX Citation
@inproceedings{Miller2019,
title = {A Taxonomy of Attacks Using BGP Blackholing},
author = {Lo{\"{\i}}c Miller and Cristel Pelsser},
year = 2019,
month = sep,
booktitle = {European Symposium on Research in Computer Security},
publisher = {Springer},
address = {Luxembourg},
series = {Lecture Notes in Computer Science},
volume = 11735,
pages = {107--127},
doi = {10.1007/978-3-030-29959-0\_6},
editor = {Kazue Sako and Steve A. Schneider and Peter Y. A. Ryan},
organization = {Springer},
abstract = {BGP blackholing is a common technique used to mitigate DDoS attacks. Generally, the victim sends in a request for traffic to the attacked IP(s) to be dropped. Unfortunately, remote parties may misuse blackholing [29, 57] and send requests for IPs they do not own, turning a defense technique into a new attack vector. As DDoS attacks grow in number, blackholing will only become more popular, creating a greater risk this service will be exploited. In this work, we develop a taxonomy of attacks combining hijacks with blackholing: BGP blackjacks (blackhole hijacks). We show that those attacks effectively grant more reach and stealth to the attacker than regular hijacks, and assess the usability of those attacks in various security deployments. We then find that routing security mechanisms for BGP [30, 31] do not provide an adequate protection against some of those attacks, and propose additional mechanisms to properly defend against or mitigate them.},
bibsource = {dblp computer science bibliography, https://dblp.org},
biburl = {https://dblp.org/rec/conf/esorics/MillerP19.bib},
groups = {International Conferences},
keywords = {BGP, Security, Blackholing, DDoS, Communities, Hijacks, Leaks},
type = {Selective conference},
x-international-audience = {Yes},
x-language = {EN}
}
Related publications
Leveraging Inter-domain Stability for BGP Dynamics Analysis
Thomas Green, Anthony Lambert, and Cristel Pelsser, et al.
Passive and Active Measurement - 19th International Conference, PAM 2018, 2018
Leveraging interdomain stability for squeezed and juicy BGP dynamics
Thomas Green, Anthony Lambert, and Dario Rossi, et al.
7th PhD school on Traffic Monitoring and Analysis (TMA), 2017
The BGP Visibility Toolkit: Detecting Anomalous Internet Routing Behavior
Andra Lutu, Marcelo Bagnulo, and Cristel Pelsser, et al.
IEEE/ACM Transactions on Networking, 2015
Protection contre les fuites de données : un environnement micro-services sécurisé
Loïc Miller, Pascal Mérindol, and Antoine Gallais, et al.
CoRes, 2021